The Latest Phishing Attacks Against Businesses Are Becoming More Audacious
phishing attacks, cybersecurity, Microsoft Defender, threat report, business security, cybercrime, phishing strategies, corporate cybersecurity, information security
## Introduction
In the fast-evolving landscape of cybersecurity, one type of cyber threat continues to plague businesses around the globe: phishing. The recent threat report released by Microsoft Defender sheds light on the increasingly audacious strategies employed by cybercriminals targeting corporate systems. As businesses integrate more advanced technology into their operations, attackers are relentlessly adapting their tactics to exploit vulnerabilities, making it imperative for organizations to stay vigilant.
## Understanding Phishing Attacks
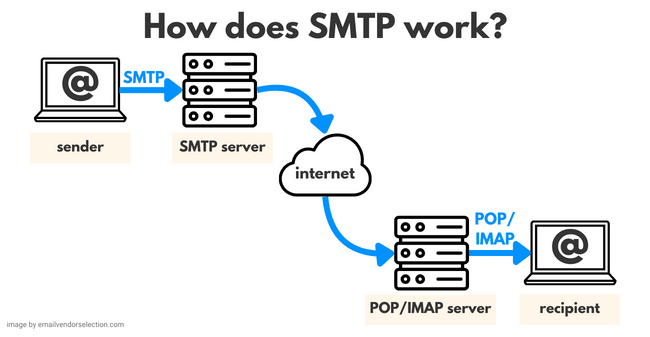
Phishing attacks are deceptive tactics used by cybercriminals to trick individuals into divulging sensitive information, such as usernames, passwords, and financial details. These attacks are commonly executed through emails, social media, or websites that mimic legitimate entities. The sophistication of these scams has grown over the years, making it increasingly difficult for employees and even security systems to identify threats.
### The Rise in Phishing Incidents
According to Microsoft Defender's recent findings, phishing incidents have surged, and the strategies being employed have become alarmingly creative. Cybercriminals are no longer relying on generic emails but are now using tailored approaches that leverage personal information to lend credibility to their schemes. This rise in personalized phishing attempts, known as spear phishing, poses a significant risk to corporate security.
## The Bold New Tactics of Cybercriminals
### Social Engineering Techniques
One of the standout features of the latest phishing attacks is the utilization of advanced social engineering techniques. Cybercriminals are increasingly employing psychological manipulation to create a false sense of trust. They may pose as a trusted colleague or a reputable institution, making it easier for them to gain access to sensitive information. By exploiting human emotions such as fear, urgency, or curiosity, attackers can effectively bypass traditional security measures.
### Use of Technology
Additionally, the integration of new technologies has enabled cybercriminals to enhance their phishing tactics. For instance, artificial intelligence (AI) is being used to generate more convincing emails that can easily deceive employees. The inclusion of personalized details, such as the recipient's name or recent company activities, adds another layer of authenticity, making phishing attempts harder to detect.
### Multi-Channel Attacks
Moreover, attackers are diversifying their approach by employing multi-channel attacks. This means that they are not only targeting individuals via email but also leveraging social media platforms and messaging apps to reach potential victims. The interconnected nature of digital communication allows these criminals to create a more comprehensive attack strategy, increasing their chances of success.
## The Impact on Businesses
### Financial Losses
The implications of these audacious phishing attacks extend far beyond the immediate loss of data. The financial ramifications can be devastating, with companies facing substantial losses due to fraud, data breaches, and remediation costs. Furthermore, the reputational damage incurred from a successful phishing attack can cripple a business, leading to a loss of customer trust and a decline in market share.
### Regulatory Consequences
In addition to financial losses, businesses may also face regulatory consequences as a result of a data breach. Many industries are subject to strict regulations regarding data protection and privacy. Failing to safeguard sensitive customer information could lead to hefty fines and legal repercussions, compounding the financial impact of a phishing attack.
## Strengthening Defenses Against Phishing
### Employee Training and Awareness
With the evolving nature of phishing attacks, employee training and awareness have never been more critical. Organizations must invest in regular training sessions to educate employees about the latest phishing tactics and how to recognize them. This proactive approach can significantly reduce the likelihood of falling victim to such scams.
### Implementing Multi-Factor Authentication
In addition to training, implementing multi-factor authentication (MFA) can provide an additional layer of security. MFA requires users to verify their identity through multiple means, such as a password and a biometric scan or a one-time code sent to a mobile device. This added step can deter cybercriminals, even if they manage to obtain login credentials through phishing.
### Regular Security Audits
Conducting regular security audits is essential for identifying vulnerabilities within the organization. By assessing current security measures and ensuring they are up to date, businesses can better protect themselves against phishing attacks. Utilizing advanced security solutions, such as email filtering and threat detection systems, can also enhance defenses.
## Conclusion
As highlighted by Microsoft Defender's latest threat report, the audacity and originality of phishing attacks against businesses continue to escalate. Cybercriminals are becoming increasingly sophisticated, employing advanced techniques that exploit human emotions and technology to achieve their goals. In this challenging environment, it is crucial for organizations to prioritize cybersecurity by investing in employee training, implementing multi-factor authentication, and conducting regular security audits. By taking these proactive steps, businesses can bolster their defenses and mitigate the risks associated with phishing attacks, safeguarding their assets and maintaining customer trust in an ever-evolving digital landscape.
Source: https://www.muyseguridad.net/2026/03/06/los-nuevos-ataques-de-phishing-contra-empresas-son-cada-vez-mas-audaces/